Archives
Here are all the past articles.
OWASP
I: Abuse of FunctionalityII: Exploitation of Authentication
III: Injection
IV: Injection Part II
Data Forensics
PhotorecWindows
Kali
NiktoJohn the Ripper
Shred
Burp Suite Set Up Tutorial Small Intruder
I: Wireshark
Web App Vulns
SubdomainsBaker's Dozen
Etcetera
One Time PadPHP Backdoor File Analysis
Hiring Procedures
SPF and Email Spoofing
Burp Suite Set Up Tutorial Small Intruder
Burp Suite is a need to know tool for people looking to be more effective in their web app pen testing. Burp has set of tools that will helpHere is how to get it set up.
Visit:
https://portswigger.net/burp/download.html
It is a Java program, so you will need a run time environment installed. Here
Find a home directory for your jar file and fire it up with a double click or else you can start it with cmd and allocate the JRE some extra memory (2gb)
java -Xmx2g -jar C:\directory\burpsuite.jar
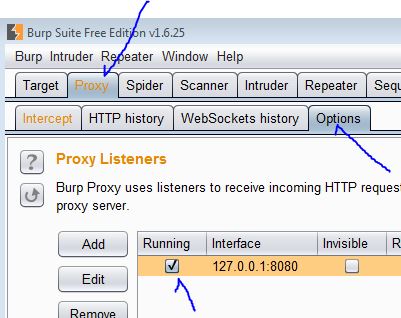
We will set up the Proxy settings first.
If you know what a Proxy is, skip over
-----------
So why do you need to set up this proxy? To intercept traffic of course.
Here is a simplified way to think of it. Normal internet traffic goes like this:
Browser --> Web Server
Now with a proxy set up
Browser --> Proxy --> Web Server
Not a complicated idea.
-----------
Now that the proxy is up and running you need to point your browser to the proxy.
For this step I recommend downloading a browser you don't normally use, Firefox or Chrome, that can just be your 'Burp browser' and not worry about having to roll settings around so much.
In Firefox,
Tools -> Options -> Advanced -> Network -> Settings
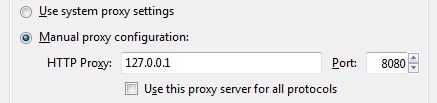
Match the IP and Port to what Proxy listeners are set up in your instance of Burp.
Check to see if it works!
visit http://burp
or visit another site and check to see if HTTP history tab is populating while visiting sites.
Now HTTP traffic will go through fine, but we need to get HTTPS set up as well.
Visit http://burp and click CA Certificate, download the cert.
Now install the Cert:
For Firefox:
Tools -> Options -> Advanced -> Certificates -> View Certificates -> Import -> (Select the Burp Cert) -> "Trust this CA to id websites - > Ok -> Ok -> Restart Firefox
Now you can visit HTTPS sites.
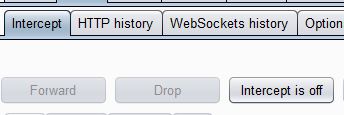
You might notice that your traffic has stopped, You click around the web and nothing is happening, check the Intercept is turned off, at least until you need it.
--------------------------------
Navigate to the URL you want to play with, turn on the Interceptor and capture some info, turn off the Interceptor. Check Proxy->HTTP history and see the list of URLs.
Ensure the Parameters check box is true and right click to see the plethora of options:
Click on the "Send to Intruder"
Target: confirm the target url/port
Positions: Attack type: Sniper, clear all selections. Then highlight the one or two parameters you want to play with and click the Add button the right.
Payload/Options really depend on what it is you are trying to do. I'm a slouch, so XSS it is, but Burp doesn't have a native XSS detection, but these folks made a nice extension. I recommend trying it out.
https://blog.nvisium.com/2014/01/accurate-xss-detection-with-burpsuite.html
Don't be scared, added an extension is very easy.
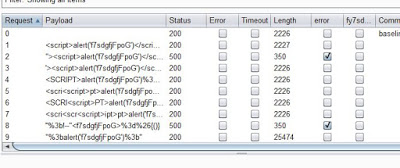
After all the options are set up, fire away! Click on start attack and go watch a movie, cause you have the demo and that means your attacks are time throttled!
I'm still getting used to all that Burp has to offer, so expect more robust tutorials in the future.
If you know what a Proxy is, skip over
-----------
So why do you need to set up this proxy? To intercept traffic of course.
Here is a simplified way to think of it. Normal internet traffic goes like this:
Browser --> Web Server
Now with a proxy set up
Browser --> Proxy --> Web Server
Not a complicated idea.
-----------
Now that the proxy is up and running you need to point your browser to the proxy.
For this step I recommend downloading a browser you don't normally use, Firefox or Chrome, that can just be your 'Burp browser' and not worry about having to roll settings around so much.
In Firefox,
Tools -> Options -> Advanced -> Network -> Settings
Match the IP and Port to what Proxy listeners are set up in your instance of Burp.
Check to see if it works!
visit http://burp
or visit another site and check to see if HTTP history tab is populating while visiting sites.
Now HTTP traffic will go through fine, but we need to get HTTPS set up as well.
Visit http://burp and click CA Certificate, download the cert.
Now install the Cert:
For Firefox:
Tools -> Options -> Advanced -> Certificates -> View Certificates -> Import -> (Select the Burp Cert) -> "Trust this CA to id websites - > Ok -> Ok -> Restart Firefox
Now you can visit HTTPS sites.
You might notice that your traffic has stopped, You click around the web and nothing is happening, check the Intercept is turned off, at least until you need it.
--------------------------------
Navigate to the URL you want to play with, turn on the Interceptor and capture some info, turn off the Interceptor. Check Proxy->HTTP history and see the list of URLs.
Ensure the Parameters check box is true and right click to see the plethora of options:
Target: confirm the target url/port
Positions: Attack type: Sniper, clear all selections. Then highlight the one or two parameters you want to play with and click the Add button the right.
Payload/Options really depend on what it is you are trying to do. I'm a slouch, so XSS it is, but Burp doesn't have a native XSS detection, but these folks made a nice extension. I recommend trying it out.
https://blog.nvisium.com/2014/01/accurate-xss-detection-with-burpsuite.html
Don't be scared, added an extension is very easy.
After all the options are set up, fire away! Click on start attack and go watch a movie, cause you have the demo and that means your attacks are time throttled!
I'm still getting used to all that Burp has to offer, so expect more robust tutorials in the future.